Комментарии:

I missed an example showing how to not use JWT in sessions
Ответить
Excellent video. What is the ideal way to authenticate and authorize these days?
Ответить
thanks for explanation
Ответить
informative
Ответить
Thank you for this explanation
Ответить
Amazing animation.
Ответить
As third party cookies are being deprecated in favor of FedCM, even with JWT we will not be able to implement SSO around mid 2024.
JWT can still be used for logins without SSO though.

Important thing to remember, is that when an user logs out, the JWT is still usable. The log out process just removes it from client cookies/local storage. So unless the server application has implemented token blacklisting on logout, a malware can still use the jwt till it expires.
Ответить
Thank you!
Ответить
WHY DO KILLER PUTIN'S SCIENTISTS HAVE ACCEESS TO JWT DATA??? Western Democratic Societies Spend $10 Billion+ and His Freak Show gets Free Access. What the Hell Good are Sanctions IF YOU DON'T PUNISH THE RUSSIAN PEOPLE?
Ответить
Don't use JWT. Its just overhead that serves no benefit and makes your life more complex. Spend your time on security hardening on your server. Crazy idea designed by clever people focused on their front end skills, with insufficient backend experience designing extremely secure systems.
Ответить
one antipattern i witnessed is to put stuff into the payload that would rather belong into a rest path. like a for example GET for a particular resource where the resource key/resource had to be provided via payload instead of rest path. there is potential for missuse like that too, not only security.
Ответить
wow so much information /s
Ответить
This is a good intro to JWTs. Although, I do think that JWT, oauth and oidc is being somewhat mixed together. JWT's does not necessarily provide authorization or authentication. JWT is just a standard for signing JSON claims.
Ответить
I still prefer custom access tokens to jwt.
Ответить
i always pronounced them jay double u tees. first time i am hearing joughts lol
Ответить
Really clear, concise explanantion.
Ответить
Nice video
Ответить
This is an absolutely amazing channel.
Ответить
Great video, everything was well explained, thanks!
Ответить
Couldn't agree more. Session management with JWT was a problem for me in a project because for one of the clients they wanted only one active session for a user.
Ответить
It amazed me when I heard it is pronounced as "jot"
Ответить
V good
Ответить
Nice video, but I'd love to see comparison with cookies, for example cookies are used as default session store in Rails and can be stateless as JWT
Ответить
You do assume that the token is generated server side, which is not always the case. If your client is a mobile app, then it is much better if you generate the token on the client. The mobile app generates a new token for every new call, signing the token with the private key. The token would then be verified with the public key. The pair (private/public key) is generated during the sign up/sign in process. The public key is stored on the server, the private key in stored on the device keychain. No replay attack is possible in this configuration. Implemented for two different apps, first time 6 years ago. Most people creates a server side token, which is not as secure, because you can steal the token. And generally this token expires after days, otherwise you would have to issue a new token, and maybe ask to relogin every day, which is really annoying.
Ответить
I don't like to enconde user data in JWT...specially if you have to send roles and permissions
Ответить
It doesn't make any sense to suggest hijacking is a failure of JWT ("vulnerable to theft") since it's just an access token (with verifiably authentic user information). Access tokens could be hijacked as well, so it's no better or worse than the alternatives as a Bearer token. ☝🤔
Ответить
Really good, understandable explanation (plus your superior graphics)! Thanks! 😎✌️
Ответить
What do you use for these animations?
Ответить
I still fail to understand the security part of JWTs. If they are sent as unencrypted headers and can be easily stolen why should we rely on them for user authentication and by consequence for authorization?
Ответить
Thanks
Ответить
Thank you so much for this video🙏🏻
Ответить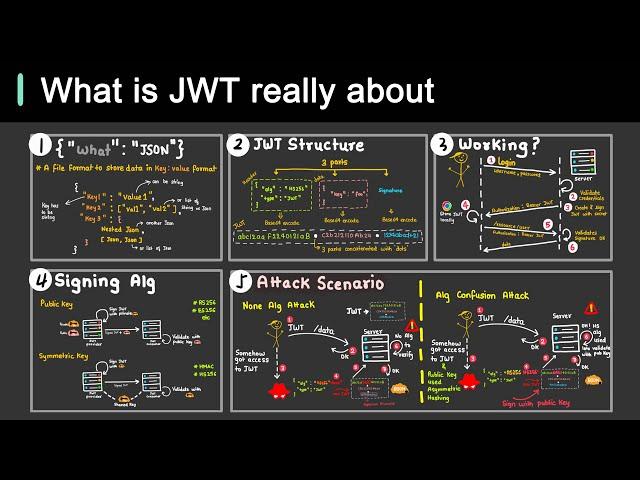


![[MULTI SUB] "Sad Love" [New drama] What should I do if my little wife has terminal cancer? [MULTI SUB] "Sad Love" [New drama] What should I do if my little wife has terminal cancer?](https://ruvideo.cc/img/upload/Y1RwMnhJT3Q5S0o.jpg)




















