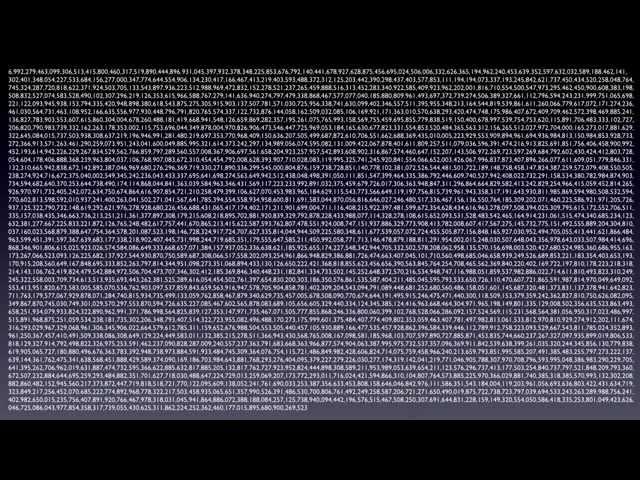
How the RSA algorithm works, including how to select d, e, n, p, q, and φ (phi)
Комментарии:

Could not get the answer for p=23, q=19, and e=283 with the steps. Can someone try n lmk?
Ответить
π
Ответить
A simple trick to get the d as well: d = e-1 mod φ(n). Let's take the example in the video:
e = 7
φ(n) = 40
7^-1 mod 40 = 23
and that's how you can get it without going through the steps of the Extended Euclidean Algorithm

How to choose e, just a small prime that doesn't share a factor with φ(n) ?
Ответить
I would make a big distinction in RSA between asymmetric encryption and public-key encryption. If you use a well-known and small 'e', you have public key, but can't support 'asymmetric' key encryption. With 'asymmetric' key encryption, 'e' and 'd' have the same properties; and are equally secret.
I use it to make digitally signed tokens such that you don't know the plaintext until you produce a witness that you performed verify to extract a secret to decrypt the signed claims. That way, the signer distribute the verify key to those who are allowed to VERIFY. It's not totally public, because it's (n,e), but signer has (n,d,e). This allows tokens to be passed around so that man-in-the middle can't decode the claims, and the verifier can only extract verified claims. ie: the current way of checking signatures (plaintext,Sign(H(plaintexty))=sig) has security problems. The main one being that you allow people to not verify the signatures; something that is very common in the hands of web developers. And the other is in leaking the tokens to intermediate proxies.

thats fun stuff
Ответить
I have used your way finding D but I ended up with zero instead of 1. my number was p=5 and q=13 and e=35 I was not able to get a correct answer, I don't know why?
Ответить
Thank you for making this easy to understand! I am no good with math but I like to be able to use it from time to time! 😀
Ответить
For MOD-Inverse - Use pow() the built-in function in Python3.8 - e.g. d = pow(e, -1, (p-1)*(q-1) )
Ответить
Thanks for this.
Ответить
Thank you this was very helpful
Ответить
Thank you, I got stuck implementing the RSA in Python at "d". your calculation path was easy to implement.
Ответить
Best explanation ever.. Thank you.
Can I get the video for Elliptic Curve Cryptography, from you, please?

Stellar video
Ответить
Thank the lords for this video!
Ответить
This has to be one of the best if not the very best explanation of the RSA algorithm that i've come across, Thank you!
Ответить
tnkz bud
Ответить
OMG! so I am being taught Maths in uni and its basically everything in this getting me ready for next year. I find it hard to follow the lecturer sometimes and this is amazing! I need to also program a crypto algorithm and this gives me a good base! THANK YOU!
Ответить
Amazing
Ответить
Thank you
Ответить
how is 40 ÷ 7 = 5? my calculator and my brain says it's 5,714....
Ответить
what if i have something like phi- 24 and e- 11??
Ответить
what is mod!??!
Ответить
This is hands down the best RSA video out there. Too bad it took me so long to find it >.<
Ответить
Allez Adams
Ответить
Je t'aime
Ответить
Thanks for this terrific explanation.
Ответить
so great, very well explained, thank you so much.
Ответить
You're the best!
Ответить
this video is PERFECTION
Ответить
Very well explained
Ответить
i love u man
Ответить
Best explanation 👍
Ответить
Good explanation, but is important to point that e must be coprime with phi and N. With small numbers, it's relatively easy to pick a value for e, but if p and q have 30 digits each...
Ответить
Now if someone would just do a video of how to use this on a message of arbitrary length in C or Python that was easy to follow for someone learning to code.
Ответить
Simply Superb Job.... Want to give 1K likes
Ответить
u made my day & saved my time & I love you
not rly but great video & u explained everything so well & simply that even I could follow & now I wrote a working python script & I'm happy ^^

Interresting content but boring presentation.
Ответить
I've knocked together a primitive Python implementation of this and I've got two problems so far. One is that the algorithm to derive d occasionally results in a divide-by-zero error, which I've solved simply by scrapping it and starting over with a new value of e. It's still quick but there must be a more elegant solution to avoid the error in the first place?
The second problem is that, for anything more than three-digit values for p and q, the actual encryption and decryption is incredibly slow. For four-digit values it clocks in at almost a minute and a half. Why is it so slow when this process happens routinely for much larger primes than anything I'm using?

|x|
Ответить
Can somebody please explain to me how the message doesn't lose information when you calculate modulo n? As modulo is not an injective function?
Ответить
thank you, your explanation was just great.
Ответить
you are amazing!!! good work, you got a new sub
Ответить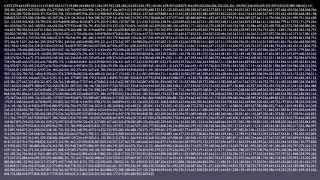


![[시즌3] 고고다이노 모아보기 24~26화 | 이어보기 | 연속보기 | 30분 | 30분보기 | 고고다이노 공룡탐험대 | 공룡 | 공룡송 | 고르고놉스 [시즌3] 고고다이노 모아보기 24~26화 | 이어보기 | 연속보기 | 30분 | 30분보기 | 고고다이노 공룡탐험대 | 공룡 | 공룡송 | 고르고놉스](https://ruvideo.cc/img/upload/RXV4MFhfUENJRmg.jpg)





















